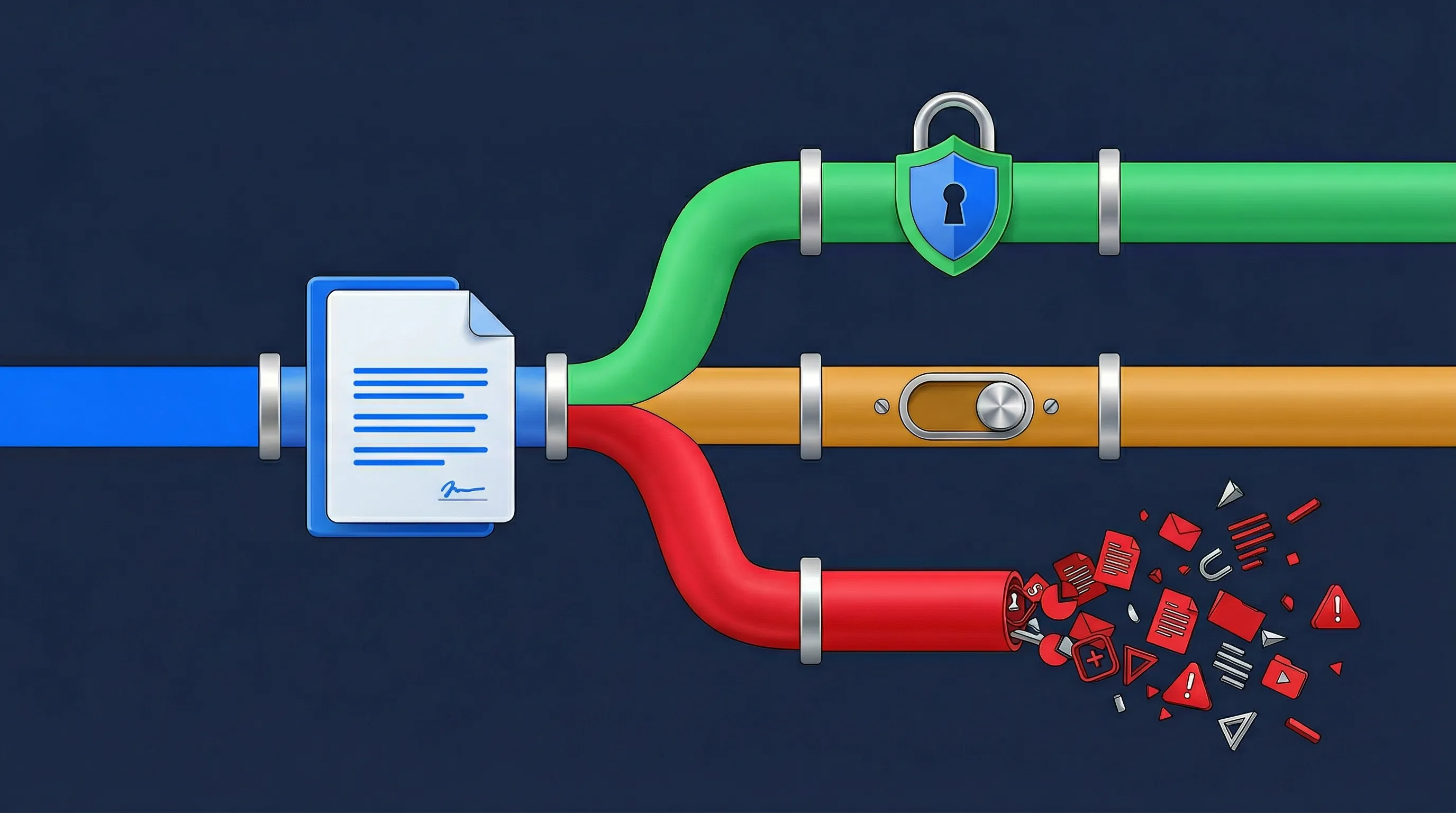
When you procure an AI SaaS tool, you are not just buying software. You are establishing a permanent, high-velocity data supply chain.
The core friction for mid-market deployers is the convergence of the EU AI Act and GDPR Chapter V.
Data residency is not data sovereignty. Using US-based cloud infrastructure creates supply chain dilution. It exposes your data to foreign jurisdictions via the US CLOUD Act.
If a vendor routes your internal corporate data to external servers for processing, the liability rests entirely on your organization. You cannot outsource this governance.
The Corporate Exhaust Analogy
Allowing an AI vendor to train their models on your internal data is like hiring a catering company for a private board meeting.
Later, you discover they recorded your strategic conversations to sell as an audiobook.
You paid them for a service, but they monetized your proprietary exhaust. In the AI era, your prompts are your intellectual property.

Vet the Vendor Data Processing Agreement (DPA)
Use the screener below to evaluate the vendor terms of service before signing the contract.
Generate a formal Vendor AI Risk Attestation to attach to your internal procurement ticket.
Privacy By Design: This executes entirely in your browser. We never see your responses.
1. The Ingestion Trap (Model Training)
According to the vendor terms of service, do they use customer inputs to train or improve their own foundational AI models? Example: Prompts and uploaded files.
Data Security Note: Your selections stay right here on your screen.
2. The Geographic Pipeline (Inference Data)
Where does the actual compute and inference processing of the AI workload take place?
Routing inference data outside the EU triggers immediate GDPR Chapter V and Schrems II liability. This applies even if the vendor promises zero data retention.
Privacy Note: We do not track your answers.
3. The Retention Window
How long does the vendor store the prompts and generated outputs on their servers?
Data Sovereignty Lock: We do not transmit, sync, or store your response.
Security Note: What you type stays on your machine.
Procurement Attestation Record
Privacy Note: Once you close your browser, all of your responses will be lost. We do not store or sync your responses on our servers.
Disclaimer: This structural mapping acts as a preliminary screening tool for vendor evaluation. It does not replace a formal Data Processing Agreement (DPA) review or a Transfer Impact Assessment (TIA) under GDPR. Consult licensed EU privacy counsel.